How Anonymous is attacking Mastercard et al.
During lunch I was browsing the web and catching up on the news, when I saw this image on an article by TechEye.net:
Apparently it is a call-to-arms flyer for Operation Payback which is being run by Anonymous and is an exercise in “retribution” against those companies and organizations seen to be censoring Wikileaks. What caught my eye was the statement towards the end of the flier:
Set your LOIC HIVE server to
loic.anonops.net, channel #loic
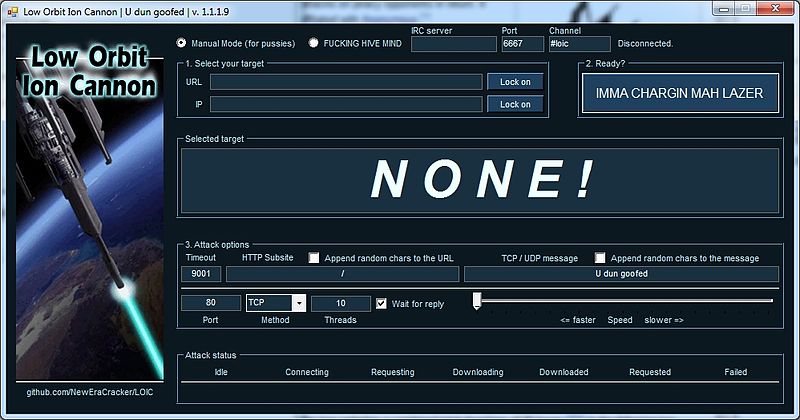
Curious, I did a Google search and discovered that LOIC is the “Low Orbit Ion Cannon”, a piece of software that floods a target server with TCP, UDP or HTTP requests. What is particularly scary is the simplicity of it’s user interface:
But it gets worse… LOIC features something called the HIVEMIND. This allows a user to turn over control of their LOIC app to a remote user, effectively it becomes a node on a “voluntary botnet” !
Listening to an IRC command channel a LOIC instance will obey commands such as:
!lazor targetip=127.0.0.1 message=test_test port=80 method=tcp wait=false random=true !lazor start !lazor stop
Needless to say anyone installing LOIC is taking several risks, firstly by installing software with dubious origins but more importantly by giving control to an anonymous group who are then performing DDOS attacks with their machine which is illegal in most countries.
It will be interesting to see how these attacks play out in the next few days and if they will be recorded as the battles of the first real cyberwar.